Cybersecurity researchers have shed more light on a remote access trojan (RAT) known as Deuterbear used by the China-linked BlackTech hacking group as part of a cyber espionage campaign targeting the Asia-Pacific region this year.
“Deuterbear, while similar to Waterbear in many ways, shows advancements in capabilities such as including support for shellcode plugins, avoiding handshakes for RAT operation, and using HTTPS for C&C communication,” Trend Micro researchers Pierre Lee and Cyris Tseng said in a new analysis.
“Comparing the two malware variants, Deuterbear uses a shellcode format, possesses anti-memory scanning, and shares a traffic key with its downloader unlike Waterbear.”
BlackTech, active since at least 2007, is also tracked by the broader cybersecurity community under the monikers Circuit Panda, Earth Hundun, HUAPI, Manga Taurus, Palmerworm, Red Djinn, and Temp.Overboard.
Cyber attacks orchestrated by the group have long involved the deployment of a malware called Waterbear (aka DBGPRINT) for nearly 15 years, although campaigns observed since October 2022 have also utilized an updated version called Deuterbear.
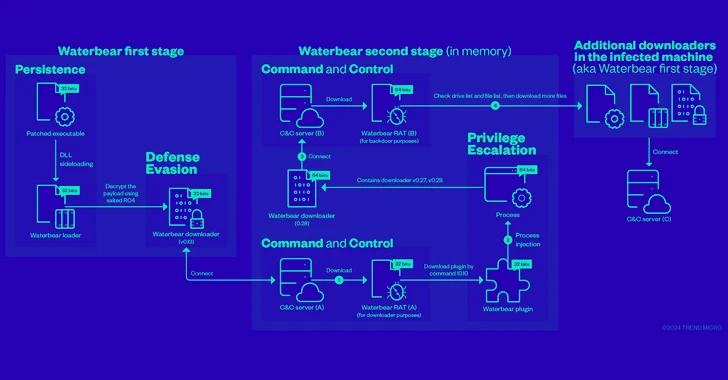
Waterbear is delivered by means of a patched legitimate executable, which leverages DLL side-loading to launch a loader that then decrypts and executes a downloader, which contacts a command-and-control (C&C) server to retrieve the RAT module.
Interestingly, the RAT module is fetched twice from the attacker-controlled infrastructure, the first of which is just used to load the Waterbear plugin that subsequently launches a different version of the Waterbear downloader to retrieve the RAT module from another C&C server.
Put differently, the first Waterbear RAT serves as a downloader while the second Waterbear RAT functions as a backdoor, harvesting sensitive information from the compromised host through a set of 60 commands.
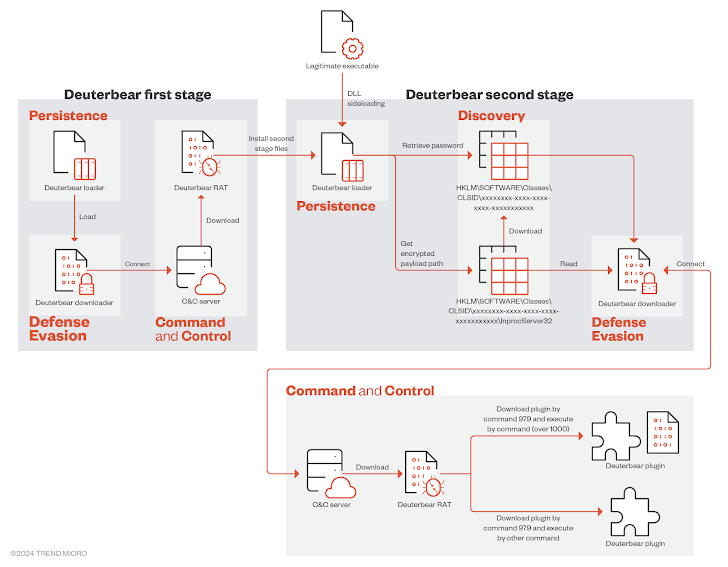
The infection pathway for Deuterbear is a lot similar to that of Waterbear in that it also implements two stages to install the RAT backdoor component, but also tweaks it to some extent.
The first stage, in this case, employs the loader to launch a downloader, which connects to the C&C server to fetch Deuterbear RAT in order to establish persistence by means of a second-stage loader via DLL side-loading.
This loader is ultimately responsible for executing a downloader, which again downloads the Deuterbear RAT from a C&C server for information theft.
“In most of the infected systems, only the second stage Deuterbear is available,” the researchers said. “All components of the first stage Deuterbear are totally removed after the ‘persistence installation’ is completed.”
“This strategy effectively protects their tracks and prevents the malware from easily being analyzed by threat researchers, particularly in simulated environments rather than real victim systems.”
Deuterbear RAT is also a more streamlined version of its predecessor, retaining only a subset of the commands in favor of a plugin-based approach to incorporate more functionality.
“Waterbear has gone through continuous evolution, eventually giving rise to the emergence of a new malware, Deuterbear,” Trend Micro said. “Interestingly, both Waterbear and Deuterbear continue to evolve independently, rather than one simply replacing the other.”
Targeted Campaign Delivers SugarGh0st RAT
The disclosure comes as Proofpoint detailed an “extremely targeted” cyber campaign targeting organizations in the U.S. that are involved in artificial intelligence efforts, including academia, private industry, and government, to deliver a malware called SugarGh0st RAT.
The enterprise security company is tracking the emerging activity cluster under the name UNK_SweetSpecter.
“SugarGh0st RAT is a remote access trojan, and is a customized variant of Gh0st RAT, an older commodity trojan typically used by Chinese-speaking threat actors,” the company said. “SugarGh0st RAT has been historically used to target users in Central and East Asia.”
SugarGh0st RAT was first documented late last year by Cisco Talos in connection with a campaign targeting the Uzbekistan Ministry of Foreign Affairs and South Korean users since August 2023. The intrusions were attributed to a suspected Chinese-speaking threat actor.
The attack chains entail sending AI-themed phishing messages containing a ZIP archive that, in turn, packs a Windows shortcut file to deploy a JavaScript dropper responsible for launching the SugarGh0st payload.
“The May 2024 campaign appeared to target less than 10 individuals, all of whom appear to have a direct connection to a single leading U.S.-based artificial intelligence organization according to open source research,” the company said.
The end goal of the attacks is not clear, although it’s suspected that it may be an attempt to steal non-public information about generative artificial intelligence (GenAI).
What’s more, the targeting of U.S. entities also coincides with news reports that the U.S. government is looking to curtail China’s access to GenAI tools from companies like OpenAI, Google DeepMind, and Anthropic, offering potential motives.
Earlier this year, the U.S. Department of Justice (DoJ) also indicted a former Google software engineer for stealing proprietary information from the company and attempting to use it at two AI-affiliated technology companies in China, including one that he founded around May 2023.
“It is possible that if Chinese entities are restricted from accessing technologies underpinning AI development, then Chinese-aligned cyber actors may target those with access to that information to further Chinese development goals,” the company said.
https://thehackernews.com/2024/05/china-linked-hackers-adopt-two-stage.html