The Android banking trojan known as Anatsa has expanded its focus to include Slovakia, Slovenia, and Czechia as part of a new campaign observed in November 2023.
“Some of the droppers in the campaign successfully exploited the accessibility service, despite Google Play’s enhanced detection and protection mechanisms,” ThreatFabric said in a report shared with The Hacker News.
“All droppers in this campaign have demonstrated the capability to bypass the restricted settings for accessibility service in Android 13.” The campaign, in total, involves five droppers with more than 100,000 total installations.
Also known by the name TeaBot and Toddler, Anatsa is known to be distributed under the guise of seemingly innocuous apps on the Google Play Store. These apps, called droppers, facilitate the installation of the malware by circumventing security measures imposed by Google that seek to grant sensitive permissions.
In June 2023, the Dutch mobile security firm disclosed an Anatsa campaign that targeted banking customers in the U.S., the U.K., Germany, Austria, and Switzerland at least since March 2023 using dropper apps that were collectively downloaded over 30,000 times on the Play Store.
Anatsa comes fitted with capabilities to gain full control over infected devices and execute actions on a victim’s behalf. It can also steal credentials to initiate fraudulent transactions.
The latest iteration observed in November 2023 is no different in that one of the droppers masqueraded as a phone cleaner app named “Phone Cleaner – File Explorer” (package name “com.volabs.androidcleaner”) and leveraged a technique called versioning to introduce its malicious behavior.
While the app is no longer available for download from the official storefront for Android, it can still be downloaded via other sketchy third-party sources.
According to statistics available on app intelligence platform AppBrain, the app is estimated to have been downloaded about 12,000 times during the time it was available on the Google Play Store between November 13 and November 27, when it was unpublished.
“Initially, the app appeared harmless, with no malicious code and its accessibility service not engaging in any harmful activities,” ThreatFabric researchers said.
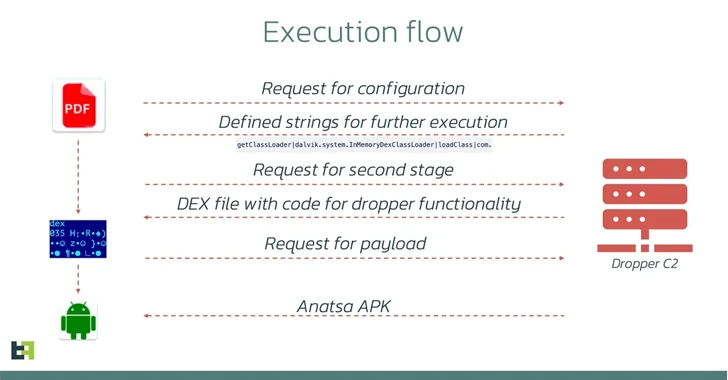
“However, a week after its release, an update introduced malicious code. This update altered the AccessibilityService functionality, enabling it to execute malicious actions such as automatically clicking buttons once it received a configuration from the [command-and-control] server.”
What makes the dropper notable is that its abuse of the accessibility service is tailored to Samsung devices, suggesting that it was designed to exclusively target the company-made handsets at some point, although other droppers used in the campaign have been found to be manufacturer agnostic.
The droppers are also capable of circumventing Android 13’s restricted settings by mimicking the process used by marketplaces to install new applications without having their access to the accessibility service functionalities disabled, as previously observed in the case of dropper services like SecuriDropper.
“These actors prefer concentrated attacks on specific regions rather than a global spread, periodically shifting their focus,” ThreatFabric said. “This targeted approach enables them to concentrate on a limited number of financial organizations, leading to a high number of fraud cases in a short time.”
The development comes as Fortinet FortiGuard Labs detailed another campaign that distributes the SpyNote remote access trojan by imitating a legitimate Singapore-based cryptocurrency wallet service known as imToken to replace destination wallet addresses and with actor-controlled ones and conduct illicit asset transfers.
“Like much Android malware today, this malware abuses the accessibility API,” security researcher Axelle Apvrille said. “This SpyNote sample uses the Accessibility API to target famous crypto wallets.”
https://thehackernews.com/2024/02/anatsa-android-trojan-bypasses-google.html